/ ¿Qué es un agente de seguridad de acceso a la nube (CASB)?
¿Qué es un agente de seguridad de acceso a la nube (CASB)?
Un agente de seguridad de acceso a la nube (CASB) es un punto de cumplimiento que se sitúa entre los usuarios de aplicaciones en la nube y los servicios en la nube para brindar protección de datos y servicios de protección contra amenazas. Los CASB previenen automáticamente la fuga de datos confidenciales, detienen el malware y otras amenazas, descubren y controlan la TI en la sombra, bloquean intercambios arriesgados, aplican políticas de seguridad como autenticación y alertas, y garantizan el cumplimiento.

¿Por qué se necesita un CASB hoy en día?
Con una mayor adopción de la nube, los CASB se han convertido en un elemento clave para la seguridad empresarial por sus diversas funciones de ciberseguridad, control de acceso y protección de datos. Le brindan control sobre los datos corporativos, tanto en movimiento como en reposo, en plataformas y aplicaciones en la nube. Los CASB son fundamentales porque:
- El crecimiento de las plataformas y aplicaciones en la nube (por ejemplo, Microsoft 365, Salesforce) ha hecho que las herramientas tradicionales de seguridad de red, como los cortafuegos en los centros de datos, sean mucho menos eficaces.
- Los equipos de TI no tienen el control que tenían antes. Casi todo el mundo puede elegir y utilizar una nueva aplicación en la nube, y el departamento de TI no puede gestionar manualmente los controles granulares de acceso de los usuarios a esa escala.
- Pueden aplicar políticas para proporcionar control de la TI en la sombra, prevención contra la pérdida de datos en la nube (DLP), gestión de la postura de seguridad SaaS (SSPM) y protección contra amenazas avanzadas.
El papel de los CASB para las empresas
Como guardianes de la actividad dentro y alrededor de los entornos de nube (ofrecen visibilidad de la actividad, aplicación de políticas de seguridad, detección de amenazas y protección de datos) los CASB permiten a las empresas adoptar la nube con confianza mientras mantienen el control y garantizan el cumplimiento normativo. Echemos un vistazo más de cerca a algunas de las ventajas de un CASB.
Ventajas de CASB
Una solución CASB eficaz ofrece ventajas clave como parte de una estrategia integral de seguridad en la nube:
Visibilidad del riesgo y la TI en la sombra
En medio del auge del trabajo remoto y el uso de dispositivos personales, las organizaciones necesitan una visibilidad clara de los usuarios, dispositivos y aplicaciones SaaS que acceden a sus entornos de nube. En esta situación, el riesgo de acceso no autorizado se dispara. Un CASB descubre el uso de aplicaciones en la nube de su organización, informa sobre el gasto en la nube y evalúa el riesgo para ayudarle a crear y mantener políticas de acceso adecuadas.
Gestión del uso de la nube
El uso de la nube puede estar sujeto a una serie de mandatos de cumplimiento, especialmente en sectores altamente regulados como los servicios financieros, la atención sanitaria y el sector público. Con un CASB, puede identificar los mayores factores de riesgo en su sector y establecer políticas estrictas de protección de datos para lograr y mantener el cumplimiento en toda su organización.
Seguridad de datos y DLP
El volumen de datos mundiales se duplica cada dos años y el riesgo de los datos crece de la misma manera. La combinación de un CASB con DLP en la nube le permite ver y corregir riesgos potenciales. Con visibilidad del contenido confidencial que viaja hacia, desde o entre entornos de nube, tiene la mejor oportunidad de identificar incidentes, hacer cumplir políticas y mantener los datos seguros.
Prevención de amenazas
En el ecosistema de TI actual, los recursos de la nube suelen ser los más vulnerables. Con el análisis de comportamiento y los datos de amenazas de un CASB eficaz, puede identificar y corregir rápidamente actividades sospechosas, mantener seguros los datos y las aplicaciones en la nube y reforzar la postura general de seguridad en la nube de su organización.
Cómo implementar un CASB
Al más alto nivel, la implementación de un CASB implica evaluar sus necesidades, hacerlas coincidir con el producto adecuado, configurarlo de la manera que mejor se adapte a sus sistemas, y realizar auditorías y supervisiones continuas. Se podría analizar en cinco pasos:
- Evalúe su entorno y establezca un plan. Comprenda los servicios y aplicaciones en la nube en uso, los riesgos asociados y sus políticas de seguridad y necesidades de cumplimiento.
- Seleccione la solución CASB adecuada para sus necesidades. Tan importante como encontrar el producto adecuado es encontrar el proveedor perfecto: elija un socio en el que sepa que puede confiar.
- Integre CASB con sus servicios en la nube y directorios de usuarios. Utilice SSO para permitir el acceso seguro de los usuarios y una autenticación perfecta.
- Configure políticas de acceso, uso compartido de datos, DLP y seguridad. En función de su sector, es posible que deba prestar especial cuidado a sus políticas de cifrado.
- Habilite la supervisión y la detección de amenazas en tiempo real. También deberá revisar y actualizar periódicamente sus políticas a medida que evolucionen las necesidades de su organización.
¿Cómo funcionan los CASB?
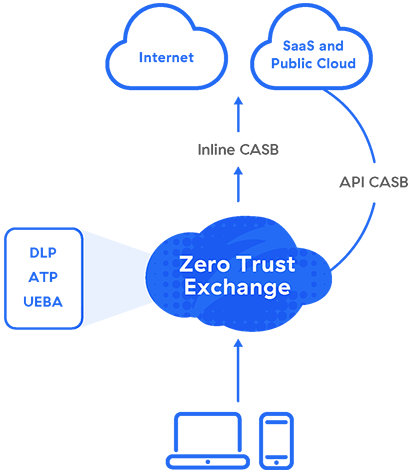
Las soluciones de CASB pueden adoptar la forma de hardware o software local, pero se proporcionan mejor como servicio en la nube para una mayor escalabilidad, menores costes y una administración más sencilla. Cualquiera que sea el factor de forma, los CASB se pueden configurar para utilizar un proxy (proxy de reenvío o proxy inverso), API o ambos: un CASB multimodo.
Proxy
Los CASB necesitan operar en la ruta de datos, por lo que el CASB ideal se encuentra en una arquitectura de proxy en la nube. Los proxies de reenvío se utilizan más comúnmente con CASB y garantizan la privacidad y seguridad de los usuarios desde el lado del cliente.
Un proxy de reenvío intercepta las solicitudes de servicios en la nube en ruta a su destino. A continuación, según su política, el CASB aplica funciones como asignación de credenciales y autenticación de inicio de sesión único (SSO), perfilado de postura del dispositivo, registro, alertas, detección de malware, cifrado y tokenización.
API
Mientras que un proxy en línea intercepta los datos en movimiento, se necesita seguridad fuera de banda para los datos en reposo en la nube, que los proveedores de CASB proporcionan a través de integraciones con las interfaces de programación de aplicaciones (API) de los proveedores de servicios en la nube.
¿Qué es un CASB multimodo?
En el modo proxy, los CASB ofrecen una aplicación de políticas en línea que detiene las fugas y el malware en tiempo real. También pueden integrarse con las API para analizar el contenido de las aplicaciones SaaS, lo que les permite encontrar y responder a patrones de datos confidenciales, así como a amenazas como el ransomware. Más recientemente, las integraciones de API se han utilizado para la gestión de la postura de seguridad SaaS (SSPM), mediante la cual los CASB remedian los errores de configuración dentro de las aplicaciones.
Los CASB que ofrecen tanto el modo proxy como el basado en API se denominan CASB multimodo. Además de proteger SaaS, pueden proteger IaaS, como Microsoft Azure y AWS S3. Y en lugar de desplegar un CASB como otro producto puntual, puede desplegarlo como parte de una plataforma SSE para garantizar una seguridad consistente, un rendimiento mejorado y una administración consolidada.
¿Qué dice Gartner sobre el CASB?
Gartner definió "CASB" por primera vez en 2012, cuando las organizaciones utilizaban principalmente la tecnología para controlar la TI en la sombra.
Los beneficios y capacidades de CASB comenzaron a superponerse cada vez más con las puertas de enlace web seguras (SWG) y, en 2019, Gartner definió el perímetro de servicio de acceso seguro (SASE), un marco de servicios en la nube que brindan “capacidades WAN integrales con funciones integrales de seguridad de red (como SWG, CASB, FWaaSy ZTNA) para respaldar las necesidades dinámicas de acceso seguro de las empresas digitales”.
En 2021, Gartner sintetizó este concepto aún más, identificando la parte de SASE centrada en la seguridad como el perímetro de servicio de seguridad (SSE). Esto refleja los crecientes esfuerzos en todo el mundo para racionalizar pilas de seguridad complejas y desarticuladas, y Gartner predice que el 30 % de las empresas habrán adoptado capacidades de SWG, CASB, ZTNA y cortafuegos como servicio (FWaaS) del mismo proveedor para 2024.
CASB y SASE
CASB y SASE se complementan entre sí: CASB protege las interacciones en la nube y los flujos de datos, mientras que SASE integra de manera más amplia la seguridad, las redes y el control de acceso en la nube. SASE incluye CASB por definición, lo que permite a las organizaciones hacer cumplir políticas y proteger datos como parte de su arquitectura de red.
Principales casos de uso para CASB
1. Descubrir y controlar la TI en la sombra
Cuando sus usuarios almacenan y comparten archivos y datos corporativos en aplicaciones en la nube no autorizadas, la seguridad de sus datos se ve afectada. Para contrarrestar esto, es necesario entender y asegurar el uso de la nube en su organización.
Zscaler CASB descubre automáticamente la TI en la sombra, revelando las aplicaciones de riesgo que visitan los usuarios. Las políticas automatizadas y fácilmente configurables aplican diversas acciones (por ejemplo, permitir o bloquear, impedir la carga, restringir el uso) en aplicaciones individuales y categorías de aplicaciones.
2. Proteger a los usuarios de SaaS no corporativos
Los usuarios pueden utilizar simultáneamente instancias sancionadas y no sancionadas de aplicaciones como Google Drive. Responder permitiendo o bloqueando la aplicación por completo puede fomentar el intercambio inapropiado de información o dificultar la productividad, respectivamente.
Zscaler CASB puede distinguir entre sus usuarios SaaS sancionados y las instancias no sancionadas que pertenecen a partes externas, gestionando la aplicación de la política adecuada a cada uno. Los controles de tenencia de SaaS preconfigurados ofrecen una reparación automatizada en tiempo real.
3. Controlar el uso compartido arriesgado de archivos
Las aplicaciones en la nube permiten un intercambio y una colaboración sin precedentes. En consecuencia, sus equipos de seguridad necesitan saber quién comparte qué en las aplicaciones autorizadas, para no arriesgarse a que partes peligrosas se hagan con sus datos.
La gestión de la colaboración es una capacidad clave de cualquier CASB efectivo. Zscaler CASB rastrea archivos de forma rápida y repetida en sus inquilinos SaaS para identificar datos confidenciales, verificar a los usuarios con los que se comparten los archivos y responder automáticamente a las acciones de riesgo según sea necesario.
4. Solucionar los errores de configuración de SaaS
Al desplegar y gestionar una aplicación en la nube, la configuración precisa es clave para garantizar que la aplicación funcione correctamente y de forma segura. Los errores de configuración perjudican su higiene de seguridad y pueden exponer fácilmente datos confidenciales.
Zscaler SSPM se integra con sus usuarios de SaaS a través de la API para analizar en busca de configuraciones erróneas que podrían poner en peligro el cumplimiento de la normativa. Es un componente de Zscaler Workload Posture junto con CSPM y CIEM.
5. Evitar la fuga de datos
Además de las configuraciones erróneas de los recursos de la nube que podrían dar lugar a infracciones y fugas de datos, es necesario identificar y controlar los patrones de datos confidenciales en la nube. Una gran cantidad de estos datos están regulados por marcos como HIPAA, PCI DSS, RGPD y muchos otros.
Zero Trust Exchange, nuestra plataforma de seguridad nativa en la nube, proporciona protección de datos unificada con capacidades DLP y CASB en la nube. Garantiza que las aplicaciones en la nube estén correctamente configuradas para detener la pérdida de datos y el incumplimiento de las normativas, mediante técnicas avanzadas de clasificación de la información para identificar y proteger los datos confidenciales allí donde estén.
6. Prevenir ataques con éxito
Una vez que un archivo infectado evita la seguridad de su organización en una de sus aplicaciones en la nube autorizadas, puede propagarse rápidamente a las aplicaciones conectadas y a los dispositivos de otros usuarios. Por eso necesita una forma de defenderse de las amenazas en tiempo real, tanto en la carga como en reposo.
Zscaler CASB frustra los avances del malware con capacidades de protección frente a amenazas avanzadas (ATP), que incluyen:
- Proxy en tiempo real para evitar que se suban archivos maliciosos a la nube.
- Análisis fuera de banda para identificar archivos en reposo y solucionar amenazas.
- Sandboxing en la nube para identificar incluso el malware de día cero
- Aislamiento del navegador en la nube sin agente para proteger el acceso desde puntos finales no gestionados.
Zscaler CASB
Zscaler ofrece CASB multimodo como servicio junto con SWG, ZTNA, etc. como parte de nuestra completa plataforma Zscaler Zero Trust Exchange™ para ayudarle a eliminar determinados productos, reducir la complejidad de TI e inspeccionar el tráfico en un solo paso. Sus administradores simplemente configuran una política automatizada para disfrutar de una seguridad uniforme en todos los canales de datos en la nube.
Seguridad en línea para los datos de la nube en movimiento
El proxy de reenvío de alto rendimiento y la inspección SSL proporcionan una protección crítica en tiempo real:
- La capacidad para descubrir la TI en la sombra y el control de las aplicaciones en la nube identifican y protegen las aplicaciones no autorizadas, sin requerir registros de los dispositivos de red.
- Las medidas de DLP impiden la carga de datos confidenciales en aplicaciones aprobadas e incluso no aprobadas.
- La protección avanzada frente a las amenazas detiene el malware conocido y desconocido en tiempo real con el sandboxing en la nube impulsado por el aprendizaje automático
- El aislamiento del navegador en la nube transmite sesiones como píxeles en el caso de los dispositivos propios para evitar la fuga de datos sin un proxy inverso.
Seguridad fuera de banda para los datos en reposo
El análisis basado en la API de las aplicaciones SaaS, las plataformas en la nube y sus contenidos mejora automáticamente su seguridad:
- Los diccionarios DLP predefinidos y personalizables identifican datos confidenciales en SaaS y nubes públicas.
- La función de gestión de la colaboración rastrea las aplicaciones para ver los archivos de riesgo que se comparten y los revoca de acuerdo con las políticas
- La tecnología de sandboxing en la nube analiza los datos en reposo para identificar y responder ante el malware y ransomware de día cero
- SSPM, CSPM y CIEM evalúan las configuraciones y los permisos de SaaS e IaaS para remediar los problemas de manera automática.
Recursos sugeridos
Preguntas frecuentes
Cualquier organización con datos y aplicaciones importantes almacenados en servicios en la nube debería utilizar un CASB. Supervisa y controla los datos enviados entre su red y la nube para garantizar el cumplimiento, evitar fugas y detener el acceso no autorizado. Los CASB ayudan a mantener la visibilidad y el control de los datos confidenciales, así como a abordar numerosos riesgos de seguridad inherentes a la nube.
Un CASB actúa como un punto de control entre su red y los servicios en la nube, supervisando y administrando el tráfico de datos hacia y desde las aplicaciones en la nube, brindando visibilidad de las actividades de los usuarios, aplicando políticas de seguridad, detectando amenazas y protegiendo datos confidenciales. Los CASB ayudan a mantener el control, el cumplimiento y la protección de datos para su entorno de red en la nube.
Para encontrar el CASB adecuado para su empresa, comience evaluando qué necesita proteger, a qué escala y qué servicios en la nube utiliza. El CASB adecuado ofrecerá una detección sólida de amenazas, controles de acceso granulares, cifrado sólido e integración con su infraestructura de seguridad y el entorno de nube existentes. Finalmente, deberá encontrar el socio tecnológico adecuado, uno en quien pueda confiar para que trabaje con usted y haga que la solución CASB que elija sea la que mejor se adapte a sus necesidades.
Muchos CASB incorporan funciones DLP para evitar que datos confidenciales pasen de su red a la nube (o viceversa) sin autorización. Las funciones DLP supervisan el tráfico de datos, bloquean o cifran datos confidenciales y envían alertas sobre posibles infracciones o fugas. Juntos, CASB y DLP ayudan a controlar el movimiento de datos y proteger la información confidencial que viaja entre redes locales y servicios en la nube.
Un CASB es una pieza esencial de una potente seguridad en la nube, pero no es la única. La seguridad eficaz en la nube combina CASB con una potente gestión de acceso e identidad, cifrado, seguridad de red, auditorías de seguridad periódicas, etc. CASB se centra en proteger los flujos de datos entre la red de una organización y la nube, pero la seguridad integral de la nube cubre una gama más amplia de amenazas potenciales en la totalidad de los aspectos de la infraestructura y el uso de la nube.



